· Alex · security · 13 min read
Understanding and Mitigating Risks with OWASP Top 10 API
Discuss API security, top 10 security risks and how to implement in your organization
OWASP Top 10 API
Today, we’re diving into the fascinating world of API security. If you’re a developer, a security professional, or just someone interested in learning about application security, then this is the perfect starting point for you.
Brief overview of API security
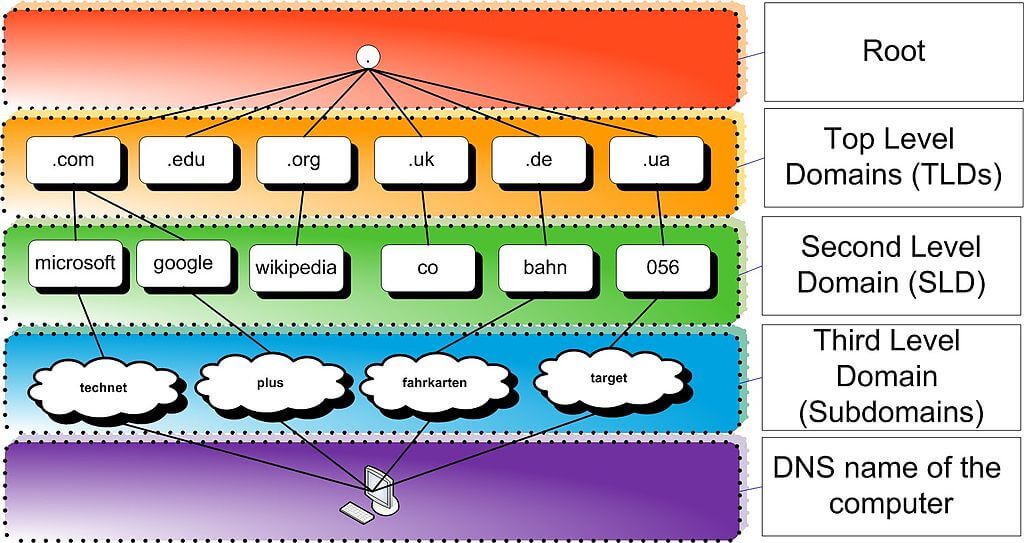
APIs, or Application Programming Interfaces, are the backbone of modern software development. They enable different applications to communicate with each other, share data, and perform various tasks. Think of APIs like a universal translator between software programs, enabling them to “speak the same language” and work together seamlessly. As you can imagine, APIs are incredibly important, and their security is crucial for the overall security of an application. API security focuses on ensuring that these communication channels are protected from unauthorized access, data breaches, and other potential threats. To put it simply, if your APIs aren’t secure, your application isn’t secure.
Introduction to OWASP and their Top 10 project for APIs
Now that you understand the importance of API security let me introduce you to an invaluable resource: the OWASP Top 10 project for APIs. OWASP, or the Open Web Application Security Project, is a nonprofit organization dedicated to improving the security of software. They’re known for their flagship project, the OWASP Top 10, which highlights the most critical web application security risks. Over the years, OWASP has expanded the scope of the Top 10 project to include APIs, acknowledging their growing prominence in software development.
The OWASP Top 10 API project aims to raise awareness about the most common API security risks, offer guidance on how to mitigate them, and promote the adoption of best practices in API security. It’s a fantastic resource for anyone looking to level up their API security game.
What is OWASP Top 10 API?
Alright, folks, now that we’ve covered the basics of API security and introduced you to the OWASP Top 10 project for APIs, it’s time to delve deeper into what the OWASP Top 10 API is all about.
Background and purpose of OWASP Top 10 API
The purpose of the OWASP Top 10 API is threefold:
- Raise awareness: By shedding light on the most critical API security risks, the OWASP Top 10 API aims to raise awareness among developers, security professionals, and decision-makers, helping them better understand the potential threats to their applications.
- Provide guidance: The OWASP Top 10 API offers detailed explanations of each risk, along with practical guidance on how to mitigate these vulnerabilities through secure coding practices, proper configuration, and other security measures.
- Encourage adoption of best practices: By promoting industry-standard best practices for API security, the OWASP Top 10 API seeks to create a more secure and robust API ecosystem.
How the list is compiled and updated
The OWASP Top 10 API is compiled by a group of security experts from various industries, who collaborate to identify and prioritize the most critical API security risks. These experts analyze data from multiple sources, including vulnerability reports, security incidents, and industry surveys, to create a comprehensive and up-to-date list of the most prevalent API security risks. The list is periodically reviewed and updated to ensure its relevance in the rapidly changing world of API security. This process involves extensive collaboration within the security community, soliciting feedback from professionals across the globe, and refining the list based on new trends, vulnerabilities, and attack vectors.
Importance of addressing these vulnerabilities in application security
Addressing the vulnerabilities outlined in the OWASP Top 10 API is essential to ensure the overall security of your application. By tackling the vulnerabilities in the OWASP Top 10 API, you can significantly reduce the attack surface of your application and mitigate the risk of a security incident.
OWASP Top 10 API Security Risks
Now that we’ve laid the groundwork, it’s time to dive into the OWASP Top 10 API Security Risks. For each risk, we’ll cover a brief explanation with examples, discuss potential impacts, and share mitigation strategies to help you secure your APIs and protect your application.
API1: Broken Object Level Authorization
- Explanation and examples: Broken Object Level Authorization occurs when an API fails to enforce proper access controls on a per-object basis, allowing unauthorized users to access, modify, or delete data. For example, if an API doesn’t verify whether a user is authorized to access a specific record, a malicious actor could exploit this vulnerability by guessing or manipulating object identifiers (e.g., user IDs, document IDs) to access unauthorized data.
- Potential impacts: This vulnerability can lead to unauthorized data access, data manipulation, or even complete data deletion, causing severe consequences like data breaches, privacy violations, and loss of trust from users or clients.
- Mitigation strategies: Implement proper access controls for each object, validate user permissions before granting access, and employ role-based access control (RBAC) or attribute-based access control (ABAC) to enforce granular authorization.
API2: Broken User Authentication
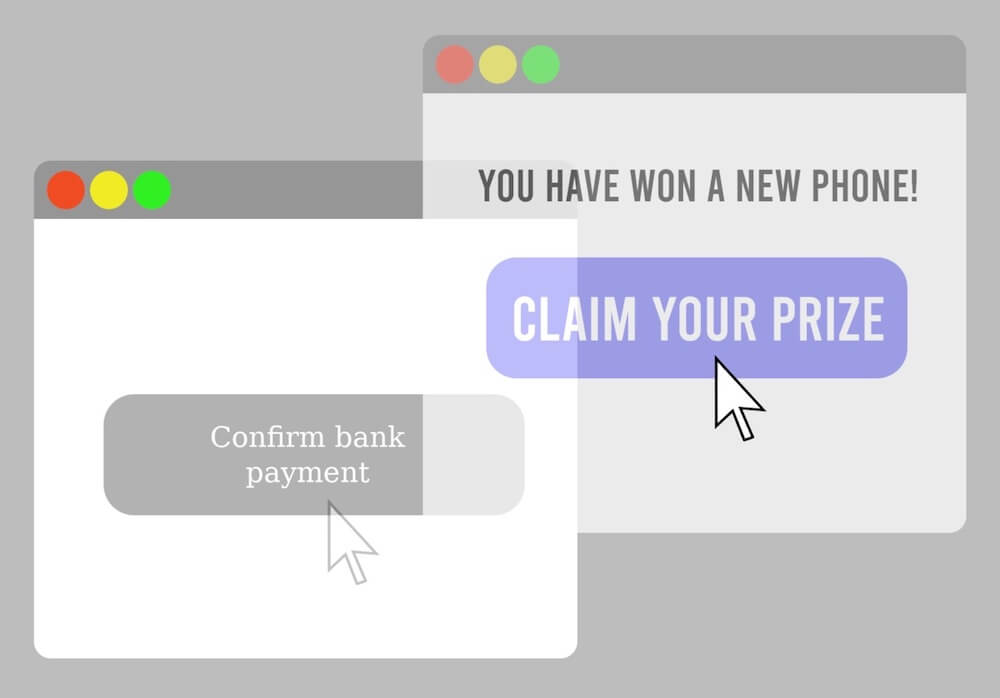
- Explanation and examples: Broken User Authentication occurs when an API’s authentication mechanisms are poorly implemented, allowing attackers to impersonate legitimate users. This could be due to weak password policies, lack of multi-factor authentication, or improper handling of tokens.
- Potential impacts: Attackers can gain unauthorized access to user accounts or perform actions on behalf of users, resulting in data breaches, identity theft, or unauthorized transactions.
- Mitigation strategies: Implement strong authentication mechanisms, enforce multi-factor authentication, use secure password storage techniques, and properly handle authentication tokens.
API3: Excessive Data Exposure
- Explanation and examples: Excessive Data Exposure refers to APIs that return more data than necessary in their responses, potentially exposing sensitive information. For example, an API might return a user’s full profile, including personal information and internal system identifiers, when only basic information is needed.
- Potential impacts: Unauthorized access to sensitive data can lead to privacy violations, identity theft, or data breaches, damaging your organization’s reputation and trustworthiness.
- Mitigation strategies: Follow the principle of least privilege, limit the data returned in API responses to the absolute minimum required, and employ data filtering or data masking techniques to protect sensitive information.
API4: Lack of Resources & Rate Limiting
- Explanation and examples: This vulnerability arises when an API doesn’t enforce limitations on the number of requests a client can make within a specific time period, making it susceptible to Denial of Service (DoS) attacks or excessive resource consumption by malicious clients.
- Potential impacts: Without rate limiting, APIs can become overwhelmed by high volumes of requests, leading to degraded performance, unavailability, or even system crashes, impacting the user experience and your application’s reliability.
- Mitigation strategies: Implement rate limiting for your APIs, use quotas to limit resource consumption, and employ mechanisms like API keys or authentication tokens to track and control client usage.
API5: Broken Function Level Authorization
- Explanation and examples: Broken Function Level Authorization occurs when an API fails to enforce proper access controls for specific functions or operations, allowing unauthorized users to perform actions they shouldn’t be able to. For example, an attacker might exploit this vulnerability to access administrative functions or execute sensitive operations without proper authorization.
- Potential impacts: Unauthorized access to sensitive functions can lead to data breaches, unauthorized actions, or even complete system compromise.
- Mitigation strategies: Enforce strict authorization checks for all functions or operations, implement role-based access control (RBAC) or attribute-based access control (ABAC) to enforce granular permissions, and regularly review and update your authorization policies.
API6: Mass Assignment
- Explanation and examples: Mass Assignment occurs when an API automatically binds incoming data to internal object properties, allowing an attacker to modify or overwrite data they shouldn’t have access to. For example, if an API allows updating a user’s profile, an attacker could exploit this vulnerability to alter other properties like user roles or access rights.
- Potential impacts: Mass Assignment can lead to unauthorized data modification, privilege escalation, or even full system takeover.
- Mitigation strategies: Use allowlists to define which properties can be updated by the API, employ proper input validation and filtering, and avoid exposing internal object properties directly in API requests.
API7: Security Misconfiguration
- Explanation and examples: Security Misconfiguration refers to insecure default settings, incomplete or ad hoc configurations, or unprotected cloud storage, which can expose your API to various attacks. For example, a misconfigured API might allow unauthorized access to debug features or sensitive data stored in cloud buckets.
- Potential impacts: Security Misconfigurations can lead to unauthorized access, data breaches, or system compromise, severely impacting your application’s security and reputation.
- Mitigation strategies: Establish a secure configuration process, regularly review and update configurations, use security-hardened system images, and apply the principle of least privilege to minimize attack surfaces.
API8: Injection
- Explanation and examples: Injection attacks occur when an API doesn’t properly validate, filter, or sanitize user input, allowing an attacker to inject malicious code or commands. Examples include SQL injection, NoSQL injection, and command injection, which can lead to unauthorized data access, data manipulation, or even system compromise.
- Potential impacts: Injection attacks can result in data breaches, unauthorized actions, or full system takeover, causing significant damage to your organization’s security and reputation.
- Mitigation strategies: Employ proper input validation, use parameterized queries or prepared statements, apply output encoding, and follow the principle of least privilege to limit potential impacts.
API9: Improper Assets Management
- Explanation and examples: Improper Assets Management refers to the inadequate tracking, documentation, or versioning of API components and resources, which can lead to security vulnerabilities. For example, outdated or unused API endpoints might remain accessible and exploitable due to improper management.
- Potential impacts: Unauthorized access to outdated or unmanaged API components can lead to data breaches, security vulnerabilities, or even system compromise.
- Mitigation strategies: Maintain an up-to-date inventory of all API components, document and version API resources, promptly retire unused or outdated components, and regularly review and update your assets management practices.
API10: Insufficient Logging & Monitoring
- Explanation and examples: Insufficient Logging & Monitoring refers to the lack of proper logging, monitoring, or alerting mechanisms to detect and respond to security incidents. For example, an API might not log failed login attempts or monitor for unusual activity patterns, allowing attackers to remain undetected.
- Potential impacts: Without proper logging and monitoring, security incidents can go unnoticed, resulting in prolonged data breaches, unauthorized access, or system compromise.
- Mitigation strategies: Implement comprehensive logging and monitoring for your APIs, establish a robust incident response plan, use intrusion detection and prevention systems (IDPS), and regularly review logs and alerts to stay ahead of potential threats.
Integrating OWASP Top 10 API in Your Application Security Strategy
In this section, we’ll talk about educating your development teams on API security risks, incorporating the OWASP Top 10 API into your security policies and guidelines, using automated testing tools and frameworks, and ensuring ongoing monitoring and updates to stay ahead of new threats.
Educating development teams about API security risks
Knowledge is power, and when it comes to application security, educating your development teams about API security risks is crucial. Start by conducting regular training sessions that cover the OWASP Top 10 API Security Risks and their mitigation strategies. Encourage open discussions and knowledge sharing, and foster a security-conscious culture within your organization.
Incorporating the OWASP Top 10 API into security policies and guidelines
To effectively integrate the OWASP Top 10 API into your application security strategy, you should incorporate it into your organization’s security policies and guidelines. This can involve creating a set of API security standards that outline how to address each of the OWASP Top 10 API risks and define best practices for secure API development, configuration, and deployment. These standards should be regularly reviewed and updated to stay current with the ever-evolving API security landscape. By establishing clear security policies and guidelines based on the OWASP Top 10 API, you can ensure that your development teams are equipped with the knowledge and tools to build secure and robust APIs.
Using automated testing tools and frameworks to identify vulnerabilities
Automated testing tools and frameworks can play a significant role in identifying and mitigating vulnerabilities in your APIs. These tools can help you scan your APIs for security issues, perform dynamic analysis, and even simulate attacks to uncover potential vulnerabilities. Some popular tools and frameworks include:
- OWASP Zed Attack Proxy (ZAP): An open-source web application security scanner and proxy tool that can be used for API security testing.
- Burp Suite: A widely used web application security testing toolkit with support for API security testing.
V. Case Studies: Lessons from Real-World API Security Breaches
In this section, we’ll examine three real-world examples of API security breaches, analyze the vulnerabilities exploited, and discuss the key takeaways and lessons learned from each case. These examples will illustrate the importance of addressing the OWASP Top 10 API Security Risks and following best practices to protect your application and its users.
Example 1: Company and vulnerability exploited
Company: Facebook Vulnerability Exploited: Improper Assets Management (API9) In September 2018, Facebook suffered a massive data breach that exposed personal information of approximately 50 million users. The breach was a result of multiple bugs in Facebook’s “View As” feature, which allowed attackers to steal access tokens and impersonate users. One of the primary causes of this breach was the lack of proper assets management, as an older, less secure version of the API was still accessible. Key takeaways and lessons learned:
- Regularly review and retire outdated API components to minimize attack surfaces.
- Implement a robust API inventory and versioning system to prevent unauthorized access to older, less secure APIs.
Example 2: Company and vulnerability exploited
Company: Uber Vulnerability Exploited: Security Misconfiguration (API7) In 2016, Uber experienced a data breach that exposed personal information of 57 million customers and drivers. The attackers exploited a security misconfiguration in Uber’s Amazon Web Services (AWS) S3 storage bucket, which stored sensitive data with public access. The API keys for accessing this data were inadvertently embedded in Uber’s GitHub repositories, allowing attackers to access the data without proper authorization. Key takeaways and lessons learned:
- Always follow the principle of least privilege when configuring access controls for your APIs and cloud storage.
- Ensure sensitive data, such as API keys and secrets, are never exposed in public repositories or insecure locations.
Example 3: Company and vulnerability exploited
Company: Panera Bread Vulnerability Exploited: Excessive Data Exposure (API3) In 2018, Panera Bread, a popular bakery-cafe chain, suffered a data breach that exposed personal information of millions of customers. The vulnerability was traced back to an API that returned excessive data in its response, including names, email addresses, physical addresses, and partial credit card numbers. The exposed API was publicly accessible, and attackers could easily exploit it by enumerating customer IDs in the API requests. Key takeaways and lessons learned:
- Limit the data returned in API responses to the minimum necessary, and ensure sensitive data is properly protected.
- Employ proper access controls and authentication mechanisms for all APIs, even those intended for internal use.
Conclusion
The rapid growth of APIs in modern applications has led to an increase in potential attack surfaces and security risks. By addressing the OWASP Top 10 API vulnerabilities, you can significantly enhance your application’s security posture, protect sensitive data, and maintain the trust of your users and clients. Implementing the mitigation strategies outlined in this post and integrating the OWASP Top 10 API into your application security strategy is crucial for building secure and robust APIs.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.