· Alex · security · 11 min read
How Does Ransomware Spread?
A few ways you might get ransomware and how to avoid it
How Does Ransomware Spread?
First of all, lets see a what are some of the entrypoints for ransomware infections:
Email and phishing campaigns
Spear Phishing:
Spear phishing is a targeted approach where the attacker does their homework on their potential victims. They’ll gather personal info about you or your organization and craft emails that look super legit. These emails might look like they’re from your bank, a coworker, or even a family member. Be extra cautious when opening emails from seemingly familiar sources, especially if they’re asking you to click on a link or download a file.
Whaling:
Whaling is like spear phishing but on steroids! It targets the big fish in the organization – think CEOs, CFOs, and other high-ranking executives. Attackers put in extra effort to create highly convincing emails and might even impersonate other senior staff members to get the job done. The goal is often to gain access to sensitive financial or company data, so always be on guard for anything suspicious.
Malicious Attachments:
Ah, the old “Hey, check out this cool file I attached!” trick. Attackers often use email attachments to spread ransomware. These files can be disguised as images, PDFs, or even Word documents. Once you open or download the attachment, the ransomware springs into action and begins to wreak havoc on your system. So, as a rule of thumb, never open attachments from unknown senders or unexpected emails.
Malicious Links:
Another popular method is sending emails with malicious links. These links might lead to a site that downloads ransomware onto your device or tries to trick you into entering sensitive information (like login credentials). Be super careful when clicking links in emails, even if they seem to be from a trusted source. Hover over the link to see the actual URL before clicking, and if in doubt, type the website’s address directly into your browser instead.
Malvertising and drive-by downloads
Exploit Kits:
Exploit kits are like a one-stop shop. They’re pre-packaged tools that automatically scan your device for vulnerabilities and then exploit them to deliver ransomware. What’s even more terrifying is that you don’t even have to click on anything – just visiting a compromised site with an exploit kit can result in a drive-by download. The best defense against exploit kits is keeping your software and operating system updated with the latest security patches. If there are no vulnerabilities to exploit, the exploit kit won’t be able to work its magic.
Compromised Websites:
Sometimes, attackers will hack into legitimate websites and insert malicious code. When you visit these compromised sites, the code executes and downloads ransomware onto your device. And it’s not just sketchy websites, either – even well-known, reputable sites can fall victim to these attacks. To protect yourself, use a reliable antivirus solution with real-time scanning and web protection features. Also, consider using browser extensions that can block malicious scripts and keep you safe while surfing the web.
Social engineering and instant messaging
Social media platforms:
Social media is where many of us spend a lot of our time, so it’s no surprise that attackers like to hang out there too. They might create fake profiles or impersonate friends and family members to send you malicious links or files. Be cautious when accepting friend requests from people you don’t know, and always think twice before clicking on links or downloading files sent to you on social media platforms.
Messaging apps:
Similar to social media, messaging apps like WhatsApp, Signal, or Telegram are not immune to attacks. Attackers can use these platforms to send malicious links, files, or even initiate scam conversations. As always, be super cautious when clicking on links or opening files from unknown contacts.
Fake software updates:
Another trick in the playbook is disguising ransomware as a software update. You might receive a message or pop-up claiming that you need to update your software, but when you click on it, you end up installing ransomware instead. To avoid this, always download software updates directly from the official website or app store, and keep your software up-to-date to minimize vulnerabilities.
Remote Desktop Protocol (RDP) and VPN Exploits:
Brute Force Attacks:
When it comes to RDP, hackers may use brute force attacks to crack your login credentials. They’ll use automated tools to try different username and password combinations until they find the right one. To protect yourself, use strong, unique passwords and consider enabling multi-factor authentication (MFA) for an extra layer of security.
Stolen Credentials:
If attackers get their hands on your VPN login credentials, they can use them to gain access to your network and spread ransomware. These credentials can be obtained through phishing attacks, data breaches, or even purchased on the dark web. Make sure you’re using strong, unique passwords and changing them regularly, and don’t forget to enable MFA.
Supply Chain Attacks:
Supply chain attacks are particularly sneaky because they exploit the trust between organizations and their suppliers or partners. Here’s how it can happen:
Software Updates:
Remember when we talked about fake software updates? Well, sometimes, attackers compromise the software update process itself. They’ll inject ransomware into legitimate software updates, so when you download the update, you’re also downloading ransomware.
Third-Party Providers:
Sometimes, third-party providers are hacked to gain access to their clients’ systems. They might compromise the provider’s software, services, or even their employees through social engineering.
Ransomware Distribution Techniques
Fileless Ransomware:
Unlike traditional ransomware, fileless ransomware doesn’t need to install any files on your system to do its dirty work. Instead, it exploits built-in tools and features of your operating system. Here’s how it works:
PowerShell and other scripting languages:
PowerShell is a super useful scripting language that comes with Windows, but it can also be exploited by fileless ransomware. Attackers use PowerShell scripts to load the ransomware directly into your system’s memory, bypassing some detection methods.
Self-Propagating Ransomware:
Self-propagating ransomware can spread from one device to another, infecting entire networks in the blink of an eye. Here are the two main ways it can accomplish this:
Worm Capabilities:
Remember those computer viruses -worms- from back in the day? Well, they’re still around, and now they’ve teamed up with ransomware! Self-propagating ransomware with worm capabilities can automatically copy itself to other devices on the same network. Once it’s on a new device, it goes to work encrypting your files and demanding a ransom.
Network Vulnerabilities:
Hackers are always on the lookout for vulnerabilities in networks that they can exploit to spread ransomware. They might take advantage of unpatched software, weak passwords, or misconfigured network settings. To protect your network, keep all software up-to-date with the latest patches, use strong passwords and multi-factor authentication, and regularly review your network configurations to ensure they meet best security practices.
Active Directory Compromise:
Attackers aim to get administrator privileges on an Active Directory (AD) managed enterprise. With this access they can disable AV/EDR, monitoring, delete backups and eventually deploy the ransomware to all computers via AD group policies.
Enterprise Software Compromise:
Sometimes compromising a particular tool is enough to deploy ransomware. There are various tools that host agents on all enterprise endpoints. For example, some EDRs have admin consoles from which you can run commands on all computers that have the agent (including running the ransomware).
Double Extortion:
In a double extortion attack, attackers not only encrypt your data but also exfiltrate some of it and threaten to expose it publicly if you don’t pay up. This one-two punch of ransomware and data breach puts even more pressure on victims to cough up the ransom.
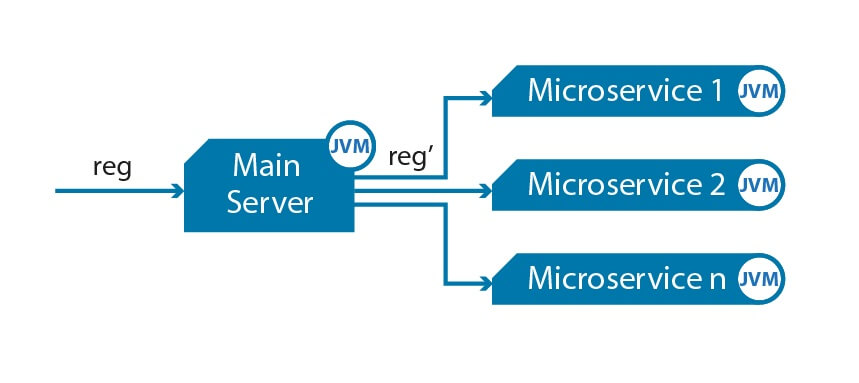
Ransomware-as-a-Service (RaaS):
RaaS is a business model where attackers provide ransomware tools and services to other criminals, often for a fee or a cut of the ransom payments. This approach has made it easier for people with limited technical skills to launch their own ransomware attacks. Here’s how it works:
Affiliate Programs:
In a RaaS affiliate program, the developers of the ransomware provide their “partners” with the tools and resources needed to carry out attacks. In exchange, the affiliates share a portion of the ransom payments they collect with the ransomware developers. This arrangement is mutually beneficial, as it allows the developers to spread their ransomware more widely while offering a way for less-skilled criminals to profit from ransomware attacks.
Customizable Ransomware Kits:
RaaS providers often offer customizable ransomware kits, which allow their “customers” to tailor the ransomware to their specific needs. These kits might include options for choosing the ransom amount, customizing the ransom note, and selecting the encryption method. By making it easy for would-be attackers to create their own ransomware, RaaS providers are further democratizing the world of cyber crime and increasing the risk of ransomware attacks for everyone.
Mitigation and Prevention Strategies:
Security Awareness Training:
Recognizing Phishing Emails:
Phishing emails are a common way for ransomware to sneak into your systems, so it’s essential to teach your employees how to spot them. Train your team to look for red flags like poor grammar, odd email addresses, and urgent calls to action. And always remind them to verify the sender’s identity and double-check any links or attachments before clicking on them.
Safe Browsing Habits:
Developing safe browsing habits is another critical aspect of security awareness training. Teach your employees to avoid visiting sketchy websites, downloading software from unofficial sources, or clicking on suspicious pop-ups. Encourage them to use strong, unique passwords and enable multi-factor authentication wherever possible.
Patch Management and Software Updates:
Software updates often include important security patches that fix vulnerabilities that attackers can exploit to spread ransomware. By ignoring these updates, you’re basically leaving the door wide open for bad actors to waltz right in. Here are some tips for staying on top of patch management and software updates:
- Make a schedule: Set up a regular schedule for checking and installing software updates on all your devices. This includes not only your computers and servers but also your routers, firewalls, and any other network devices.
- Automate updates: Many software programs and operating systems have built-in features that allow you to automate updates, so you don’t have to remember to check for them manually. Just make sure you set these options to install updates automatically, and you’ll be good to go.
- Prioritize critical updates: When you’re dealing with a large number of devices or software programs, it can be challenging to keep up with all the updates. In this case, prioritize the most critical updates, such as those that address known security vulnerabilities or fix serious bugs.
- Keep an inventory: Maintain an inventory of all your software and hardware assets, so you know exactly what needs updating and when.
Endpoint and Network Security:
Antivirus and EDR Solutions:
These tools help detect and block known ransomware threats, as well as other types of malware. But don’t stop at just antivirus software—consider investing in a modern EDR solution as well. These specialized tools can often detect and stop ransomware attacks in their tracks, even if the ransomware is a brand-new variant that your antivirus might not recognize.
Firewalls and Intrusion Detection Systems:
Intrusion detection systems (IDS) take things a step further by analyzing network traffic for signs of an attack in progress, allowing you to respond quickly and minimize the damage.
Data Backup and Recovery:
Having a solid backup strategy is like having an insurance policy for your data, ensuring that you can bounce back even if the worst happens. Let’s dive into some best practices for backing up your data:
Local and Offsite Backups:
When it comes to backing up your data, the old saying “don’t put all your eggs in one basket” definitely applies. It’s a smart idea to have both local backups (e.g., on external hard drives, NAS devices, or other storage media) and offsite backups (like cloud storage or remote servers). This way, if your local backup gets compromised or damaged, you still have a copy of your data stored safely elsewhere.
Regular Backup Testing:
Backing up your data is all well and good, but how do you know if your backups are actually working? The answer is simple: test them regularly! Schedule periodic tests to restore your data from backups to ensure that everything is working as it should. This not only gives you peace of mind but also helps you identify and fix any issues with your backup process before they become a problem.
Conclusion:
We’ve covered a wide range of ransomware distribution channels and common techniques used by attackers. By investing in security awareness training, staying on top of patch management and software updates, and employing robust endpoint and network security tools, you can significantly reduce the risk of falling victim to these threats.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.