· Alex · security · 10 min read
What are Potentially Unwanted Programs (PUP) and Their Impact on Cybersecurity
What are PUPs, how are PUPs distributed, associated risks, how to detect and prevent
Potentially Unwanted Programs (PUP)
First things first, PUPs are software programs that users often unwittingly install on their devices. They may not be as dangerous as traditional malware, but they can still be a major pain in the neck. PUPs usually come bundled with other software, hide behind misleading download links, or pose as legitimate updates. Once they find their way onto your device, they can cause a variety of issues like unwanted ads, browser hijacks, and privacy concerns. While they might not be the most vicious cyber threat out there, they can still have a significant impact on your privacy, security, and system performance. Plus, some PUPs can act as a gateway for more severe malware infections, making them a potential stepping stone for attackers.
Background and History of PUPs
Evolution of PUPs: From adware and spyware to more sophisticated threats
In the early days of the internet, PUPs were mainly adware and spyware – programs designed to display ads on your device or collect your data without your consent. However, as technology advanced and users became more security-savvy, PUPs evolved too. They’re now more sophisticated and harder to detect, often masquerading as legitimate software or hiding within software bundles. While PUPs still engage in adware and spyware activities, they have diversified to include browser hijackers and even cryptocurrency miners. As the digital landscape continues to evolve, it’s likely that PUPs will become even more complex and multifaceted in the future.
How PUPs differ from malware
Now, you might be wondering, “What’s the difference between PUPs and malware?” While both can cause harm to your device or data, the key distinction lies in the intent. Malware is specifically designed to cause harm, while PUPs are generally not as malicious. PUPs are usually more of an annoyance or inconvenience than a direct threat to your security. That being said, the line between PUPs and malware can sometimes be blurred. So, while PUPs might not be as harmful as malware on their own, they can still pose a significant risk if left unchecked.
Common types of PUPs
Let’s take a closer look at some of the most common types of PUPs you might encounter:
- Adware: Adware is software that displays unwanted advertisements on your device. These ads can be in the form of pop-ups, banners, or even injected directly into web pages. Adware is often bundled with other software and can be tricky to remove.
- Spyware: Spyware is designed to secretly collect and transmit your data without your knowledge or consent. This can include anything from browsing habits and keystrokes to personal information like passwords and credit card numbers.
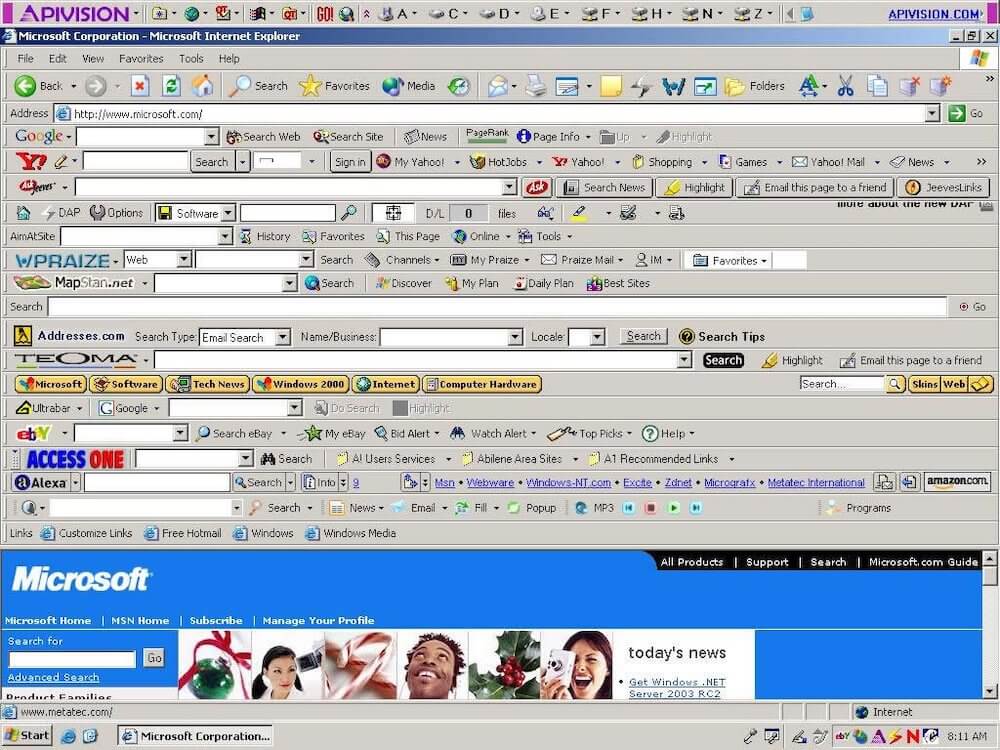
- Browser hijackers: These PUPs take control of your browser by changing its settings, such as the default search engine or homepage. Browser hijackers can also redirect your searches and inject ads into your browsing experience.
- Unwanted extensions: PUPs can come in the form of seemingly helpful browser extensions that actually do more harm than good. They can slow down your browsing experience, track your online activity, or serve unwanted ads.
- Cryptocurrency miners: Some PUPs are designed to hijack your device’s resources to mine cryptocurrency, such as Monero, without your knowledge or consent. This can lead to decreased system performance and increased energy consumption.
How PUPs Infect Computers and Networks
Social engineering techniques used by PUP distributors
- Deceptive download links: One common tactic employed by PUP distributors is disguising their programs as something else entirely. They might use misleading download links, making it look like you’re downloading a popular app or game, when in reality, you’re installing a PUP.
- Bundled software packages: PUPs often hitch a ride on other software installations, hiding within the fine print of an installer’s terms and conditions. When you install the desired software, the PUP sneaks in unnoticed. To avoid this, always choose the custom installation option (if available) and carefully review each step to deselect any additional software you don’t want. Some companies use marketing tactics like Pay-Per-Install to distribute their software.
- Fake software updates: PUP distributors can also trick you into installing their programs by masquerading as legitimate software updates. These can appear as pop-ups or in-app notifications, urging you to update your software immediately. To avoid falling for this trick, always verify the source of the update and download updates directly from the software vendor’s official website.
Technical methods of PUP distribution
- Drive-by downloads: Drive-by downloads occur when a PUP is automatically downloaded and installed on your device simply by visiting a compromised website. This can happen without any user interaction, making it a particularly stealthy method of infection.
- Malvertising: Malvertising, a combination of “malware” and “advertising,” is the practice of injecting malicious code into legitimate online ads. When you click on an infected ad, the PUP can be downloaded and installed on your device. Using reputable ad-blockers and keeping your software updated can help protect against malvertising.
- Exploit kits: Exploit kits are pre-packaged sets of tools that attackers use to identify and exploit vulnerabilities in your device’s software. Once they gain access, they can install PUPs or other malicious software without your knowledge. Regularly updating your software and using reputable security tools can help protect against exploit kits.
Signs That Your Device May Be Infected with a PUP
Slower system performance
One of the first signs that you might have a PUP lurking in your device is a noticeable decrease in system performance. PUPs can hog system resources, causing your device to slow down, freeze, or crash. If you’re experiencing sudden performance issues without an apparent cause, it might be time to scan for PUPs.
Unwanted ads and pop-ups
Unwanted ads and pop-ups can be incredibly annoying, but they can also be a sign of a PUP infection. If you’re suddenly bombarded with ads, especially ones that are intrusive or difficult to close, it’s worth investigating the possibility of a PUP on your device.
Unexpected browser redirects
Another telltale sign of a PUP infection is unexpected browser redirects. If you find that your browser is frequently taking you to websites you didn’t intend to visit or your search results are consistently hijacked, a PUP, like a browser hijacker, could be the culprit.
Installation of unwanted software
PUPs are notorious for installing additional unwanted software on your device, often without your knowledge or consent. If you notice unfamiliar programs, or browser extensions on your device, it’s time to do a thorough investigation and remove any PUPs you find.
Altered browser settings
Finally, PUPs can also alter your browser settings, such as changing your default search engine, homepage, or injecting ads into web pages. If you notice any unexpected changes in your browser settings or behavior, it’s essential to take action and eliminate any PUPs that might be responsible.
Potential Risks and Consequences of PUPs
Privacy concerns
- Data mining and personal information harvesting: Many PUPs are designed to collect data about your browsing habits, which is then sold to third-party advertisers. However, some PUPs take it a step further and harvest personal information, such as your email address, physical address, or even credit card information. This data can then be sold or used for nefarious purposes.
- Unauthorized access to sensitive information: Some PUPs can give cybercriminals unauthorized access to your device and sensitive information. This can lead to identity theft or other serious privacy breaches.
Financial risks
- Fraud and scams: PUPs can open the door to various fraud and scam tactics. For example, they might display fake warnings or error messages, tricking you into paying for unnecessary technical support or software.
- Unauthorized charges and subscriptions: Some PUPs may cause unauthorized charges by tricking you into signing up for services or subscriptions without your knowledge or consent. Always keep a close eye on your financial statements to spot any suspicious activity.
Impacts on system performance and stability
- Degraded system performance: As we’ve mentioned earlier, PUPs can take a toll on your device’s performance. They can consume system resources, leading to slower response times, decreased battery life, and increased data usage.
- Crashes and freezes: PUPs can also cause system instability, leading to frequent crashes or freezes. This can make your device frustrating to use and even result in data loss in severe cases.
PUPs as a gateway to more serious malware infections
While PUPs themselves might not be outright malicious, they can create vulnerabilities that more serious malware can exploit. For example, some PUPs can disable your device’s security features or download additional malware onto your device. This can lead to more severe infections, such as ransomware or keyloggers, which can cause significant damage and data loss.
Best Practices to Prevent PUP Infections
Maintaining updated software and operating systems
One of the simplest and most effective ways to protect your device from PUPs (and other threats) is by keeping your software and operating systems up to date. Software updates often contain important security patches that can help close vulnerabilities that PUPs and other malicious programs might exploit.
Utilizing reputable antivirus and anti-malware software
Using a reputable antivirus and anti-malware program is essential in protecting your device from PUPs and other threats. These programs can detect and remove PUPs before they have a chance to cause any harm. Just remember to keep your security software updated so it can recognize the latest threats.
Practicing safe browsing habits
Avoiding suspicious websites and downloads: Be cautious when browsing the internet and avoid clicking on suspicious links or visiting shady websites. Stick to trusted sources for your downloads, and always verify the legitimacy of a website before providing any personal or financial information.
How to Detect and Remove PUPs
Using reputable security software to scan for PUPs
The first line of defense in detecting and removing PUPs is using reputable security software. Many antivirus and anti-malware programs have built-in PUP detection capabilities, so start by running a thorough scan of your device. If the scan identifies any PUPs, follow the software’s recommended steps to remove them.
Manual removal of PUPs
- Identifying and uninstalling unwanted programs: Go through your list of installed programs and look for anything suspicious or unfamiliar. To access the list, navigate to your device’s control panel or settings, and select the option to view installed programs. Once you’ve identified any potential PUPs, uninstall them using the provided options. Keep in mind that some PUPs may use deceptive names, so do a quick search if you’re unsure about a program’s legitimacy.
- Restoring browser settings: PUPs often alter your browser settings, such as your homepage or default search engine. To restore your browser settings, access the settings menu in your browser and look for options to reset or restore the settings to their defaults. You may also need to remove any unwanted browser extensions that the PUP installed.
Conclusion
While PUPs might initially seem like minor nuisances, they can pose significant risks to your privacy, finances, and overall system performance. By understanding the nature of PUPs, their methods of distribution, and the potential consequences they bring, you’ll be better equipped to recognize the signs of an infection and take appropriate action to protect yourself. At the end of the day, it’s up to each of us to take responsibility for the security of our devices and data. Practicing good cybersecurity habits, such as keeping software updated, using reputable security tools, and staying vigilant when browsing the web, can go a long way in preventing PUP infections and other cyber threats.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.