· Alex · security · 6 min read
API Authentication Best Practices
Types, guidelines, and API authentication methods.

What is API Authentication?
API authentication is the security handshake that ensures only authorized entities get to access the precious data these APIs carry. Otherwise said, API authentication is the process that verifies an API call is coming from a legitimate source. Without effective API authentication, our data would be exposed to all sorts of cyber threats, making it a critical aspect of data privacy and security. In this blog post, we’re going to untangle the knots of API authentication - understanding what it is, why it’s essential, the different methods used, and the golden rules (or best practices, if you will) to implement it effectively.
Types of API Authentication
Why is API authentication necessary, you ask? Well, the open, interconnected nature of APIs makes them juicy targets for cyber attackers. Unsecured APIs can lead to all sorts of cyber threats, from injections to data breaches.
So, how do we make sure these digital baddies don’t get through? Enter different levels of API Authentication. Let’s break it down:
- Service to Service Authentication: This form of authentication confirms that the application trying to make the API call is legitimate.
- User-Level Authentication: This verifies that the user calling the API is legitimate.
Basic Principles of API Authentication
First up, we have the Principle of Least Privilege (PoLP). But it’s actually pretty straightforward. PoLP is like the “Goldilocks rule” of API authentication - not too much, not too little, but just the right amount of access. It means each user should have just the necessary privileges they need to carry out their tasks, no more, no less. This helps keep the risk at a minimum because even if an attacker manages to hijack a user’s credentials, they can only access limited data or functions.
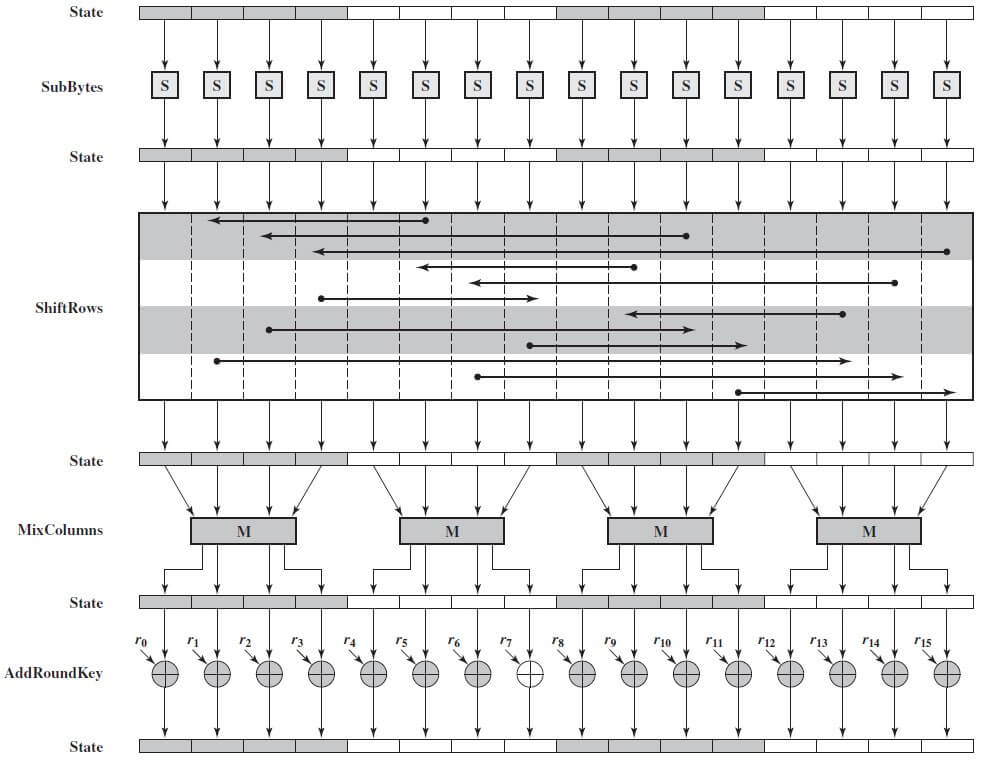
A vital security control for APIs is encryption. Encryption scrambles your data into unreadable gibberish for anyone who doesn’t have the key to decrypt it. It’s vital to ensure that your data is encrypted both in transit (while it’s moving from one place to another) and at rest (when it’s stored). In regards to APIs, encryption in transit is especially important.
Last, but not least, is using strong user authentication. No matter how secure your API is, if your users’ passwords are as weak as a wet paper bag, you’re still at risk. Encourage (or better yet, enforce) the use of strong, unique passwords. Think long, complex, and full of a mix of letters, numbers, and special characters. Multi-factor authentication is a great way to add an extra layer of protection. These principles might seem basic but you’d be surprised how often they’re overlooked. Make them the foundation of your API authentication strategy, and you’ll be well on your way to a more secure API.
API Authentication Methods
We’re moving into the meaty part of our topic now – different methods for API authentication. Each has its strengths and potential pitfalls, so it’s crucial to understand them before deciding which one suits your needs best.
Basic Authentication
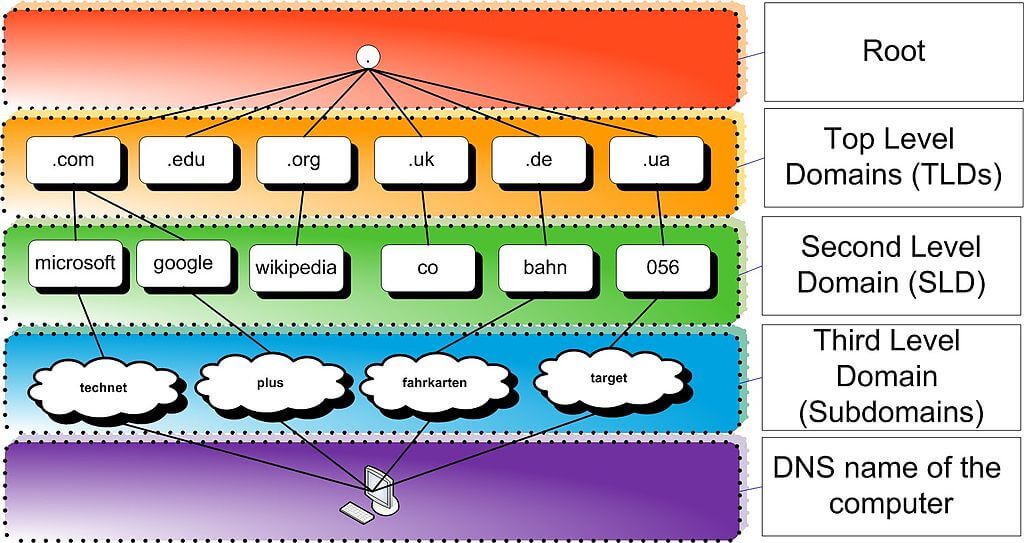
It’s the simplest form of authentication, where the client sends a username and password with each HTTP request. The server then validates these credentials and grants or denies access. Basic Auth is easy to implement, but let’s be honest, it’s like guarding a fortress with a garden fence. It lacks the security muscle needed for most applications today, and if not transmitted over HTTPS, your credentials could be easily intercepted. Hence, it’s not generally recommended for production use. Also, take a look at my post on password spraying.
Token-Based Authentication
This method uses tokens, such as JSON Web Tokens (JWT) to authenticate API calls. Here’s how it works: a client logs in with their credentials and, if valid, the server returns a token. This token is then used for future requests, proving that the client is who they claim to be. JWTs are compact, self-contained tokens for securely transmitting information. Token-based authentication provides several benefits, such as statelessness (the server doesn’t need to keep track of logged-in users) and scalability (it can handle large numbers of users). However, token management can be complex and if a token is compromised, it can provide access until it’s expired.
API Keys
An API key is a code that identifies the calling service (client) making an API call, allowing access to specific resources. They’re easy to implement and manage but can pose a serious security risk if not handled properly. They’re usually used for service-to-service authentication If an API key falls into the wrong hands, it could give attackers open access to your API. Therefore, API keys should never be hard-coded into your application, and they should be rotated and revoked regularly to minimize potential misuse. Remember, there’s no one-size-fits-all in API authentication. The right method depends on your specific use case and security needs.
Best Practices for API Authentication
Here are some guidelines:
- regularly update and rotate your API keys and tokens. This helps minimize the risk if a key or token is compromised and it’s not realized immediately.
- monitoring API usage. Keep a close eye on how your APIs are being used. Unusual patterns or spike in usage could be a red flag signaling an attack or misuse. Implement usage quotas and throttling controls to prevent any single user or service from hogging all the resources.
- rate limiting and throttling are crucial tools. These techniques control the number of requests a user or system can make within a specified time period. Think of it as a bouncer at a nightclub, limiting the number of people who can enter to prevent overcrowding.
- using an API Gateway.. This acts as a sort of gatekeeper, managing requests by enforcing throttling and security policies. It’s an excellent way to centralize your API security, ensuring that all API traffic passes through a single, secure entry point. Plus, it can take care of other tasks like collecting analytics, handling protocol conversions, and managing spikes in traffic.
- regularly audit and test your APIs for potential security vulnerabilities. Consider performing penetration testing and security audits to identify any weaknesses in your API security. Regular testing and auditing not only help you catch potential threats but also ensure your API is complying with the latest security standards and regulations. By following these best practices, you’re not just securing your API, but also ensuring it remains reliable and performant. Also, make sure to checkout my post on REST API best practices.
Conclusion
So, let’s quickly recap. API authentication is essentially the security guard of your API ecosystem, checking the credentials of each request and deciding who gets to access your data and services. It’s crucial in the grand scheme of cybersecurity, acting as a robust barrier against unauthorized access and potential cyber threats. We’ve seen the good, the bad, and the ugly of API security. Basic authentication might be easy to implement, but it lacks the security punch we need in today’s digital world. Token-based authentication and API keys can provide stronger security, but they need to be managed correctly. But when done right, robust API authentication practices can shield your data, your users, and your reputation from harm.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.