· Alex · security · 4 min read
The Ultimate Guide to File Upload Security
Guidelines, security measures and steps to securing file uploads
File Upload Security
This simple task of file uploading can be a doorway into your system, and just like any door, if left unguarded, it could invite some uninvited guests.
Understanding the Risks Associated with Insecure File Uploads
Malware Upload: This is a common and nasty tactic. Hackers can camouflage malware as innocent-looking files. Once these are uploaded and executed on your server, it’s game over.
Overwriting Critical Files: Crafty hackers can upload a file with the same name as a critical system file. If your system is not set up to handle this correctly, the uploaded file could overwrite an important system file, leading to disastrous results.
Denial-of-Service (DoS) Attacks: In this scenario, attackers flood your system with large file uploads, causing the server to exhaust resources or crash. This results in your web application becoming unavailable to legitimate users.
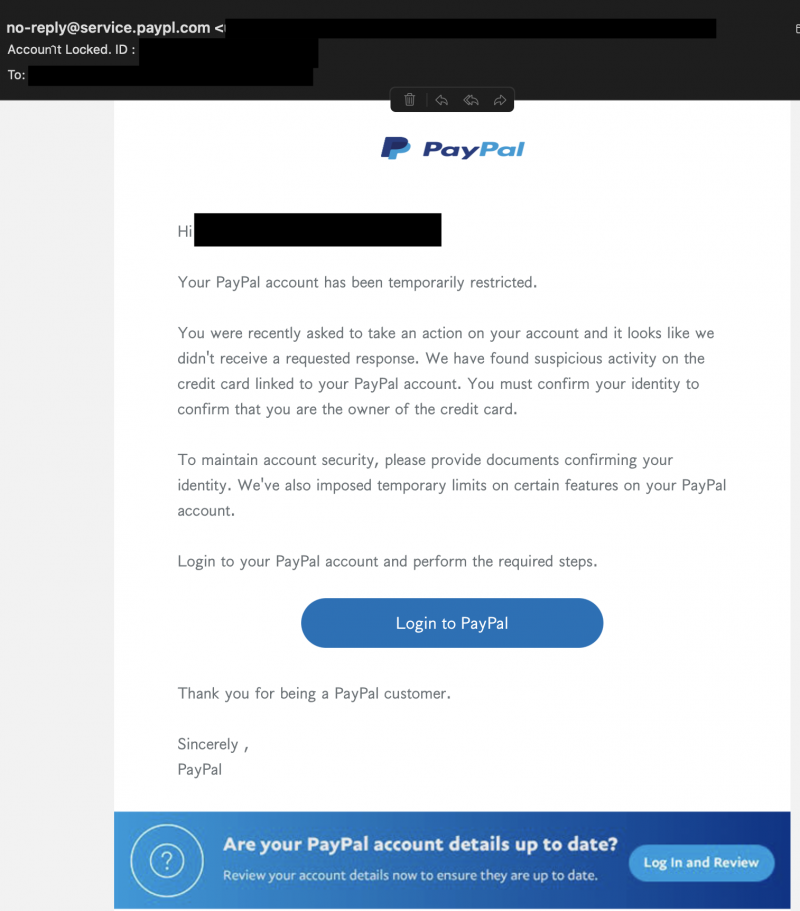
You might remember the infamous flaw in the file upload function of TimThumb, a popular WordPress plugin, which allowed attackers to upload PHP scripts disguised as image files into the system. The script acted as a backdoor, providing unrestricted access to the system to the attackers. Thousands of websites were compromised, turning a handy plugin into a nightmare.
Basic Guidelines for Secure File Upload
Limit Allowed File Types: One of the simplest ways to maintain decorum is to only allow specific file types to be uploaded, like JPEG or PNG for images, and PDF or DOCX for documents. This way, you reduce the risk of malicious files sneaking in disguised as harmless kittens. Remember, PHP files are not kittens!
Validate, Sanitize and Check File Content: All files should undergo a rigorous identity check. This means validating and sanitizing the file inputs. Make sure the file metadata, like the name and extension, doesn’t contain any suspicious characters or patterns. But don’t stop there. Go a step further and check the file content, too. There are tools out there that can help you confirm if that ‘.png’ file is truly an image and not a nasty piece of malware.
Proper Error Handling: Having proper error handling mechanisms in place is crucial. If an upload fails or something fishy is detected, the error messages should be informative enough to help you diagnose the issue, but not so detailed that they expose sensitive information about your system to potential attackers. Remember, errors should help you, not them!
Advanced File Upload Security Measures
Restrict File Size and Upload Frequency: It’s a good idea to limit the file size and regulate the frequency of uploads. This way, you not only conserve server resources but also keep potential Denial-of-Service (DoS) attacks at bay.
Use File Upload Protection Tools: There’s a wide array of security tools out there designed to protect against insecure file uploads. These include web application firewalls (WAFs), antivirus software, and specialized file upload scanning solutions.
Rename Uploaded Files: Renaming files after they’ve been uploaded can be a great way to throw attackers off the scent. By doing this, you’re essentially dismantling any code that relies on the original filename to execute. Plus, it makes it harder for hackers to locate their uploaded files.
Steps to Implement a Secure File Upload Process
So throwing all that together we have:
- Step 1: Define Allowed File Types
- Step 2: Set Maximum File Size and Upload Frequency
- Step 3: Implement File Validation
- Step 4: Rename Uploaded Files
- Step 5: Use Security Tools
- Step 6: Regularly Monitor and Update Your System
Conclusion
It’s been quite the journey, and if there’s one thing we want you to take away, it’s this: Secure file uploading is non-negotiable. In our digital age, data is the new gold, and like gold, it needs to be safeguarded. With file uploads being such a common feature in web applications, it’s a prime target for attackers looking to strike it rich.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.