· Alex · security · 11 min read
REST API Authorization Best Practices
Authorization protocols, Role-Based Access Control, securing API endpoints, auditing and monitoring, and security practices for API consumers

REST API Authorization
REST (Representational State Transfer) APIs are a popular and widely adopted standard for designing networked applications. They offer an easy-to-use, scalable, and flexible way for systems to communicate with one another, facilitating data exchange and enabling the creation of feature-rich applications. With the growing reliance on APIs to power everything from mobile apps to web services, it’s never been more important to ensure that these interactions are secure and that access to sensitive data is properly managed. That’s where authorization comes into play.
In the context of REST APIs, authorization is the process of determining what actions a user, or more specifically, an API consumer, is allowed to perform. It’s a critical aspect of API security, ensuring that only authorized users can access specific resources and perform certain operations on your API.
The Fundamentals of REST API Authorization
Understanding Authentication vs. Authorization
These two terms may sound similar, but they serve distinct purposes in the context of API security. Let’s break them down:
- Authentication: This is the process of verifying the identity of a user or an API client. In simpler terms, it answers the question, “Who are you?“. Authentication typically involves the user providing credentials, like a username and password, an API key, or a token to prove their identity.
- Authorization: Once the user’s identity is established, we move on to authorization, which determines what actions they are allowed to perform. It answers the question, “What are you allowed to do?” Authorization involves defining and enforcing access policies, ensuring that users only have access to the resources and operations they’re permitted to use.
While both authentication and authorization are crucial for securing your APIs, this blog post will focus primarily on the latter. However, it’s important to remember that these two processes go hand in hand, and a robust security strategy requires both.
The Role of Access Control in API Security
Access control is the heart and soul of API authorization. It’s all about managing and enforcing policies that dictate which users or clients can access specific resources and perform certain actions on your API. A well-designed access control system can significantly reduce the risk of unauthorized access and data breaches. When things don’t work right, it’s called broken access control. Implementing proper access control in your APIs typically involves:
- Defining roles and permissions: This involves mapping out the different user roles and the specific permissions each role should have.
- Enforcing access control policies: Once the roles and permissions are defined, you need to ensure that the API correctly enforces these policies for every incoming request.
- Regularly reviewing and updating policies: As your API evolves, so should your access control policies. Regularly review and update them to keep up with any changes in your API’s functionality or user base.
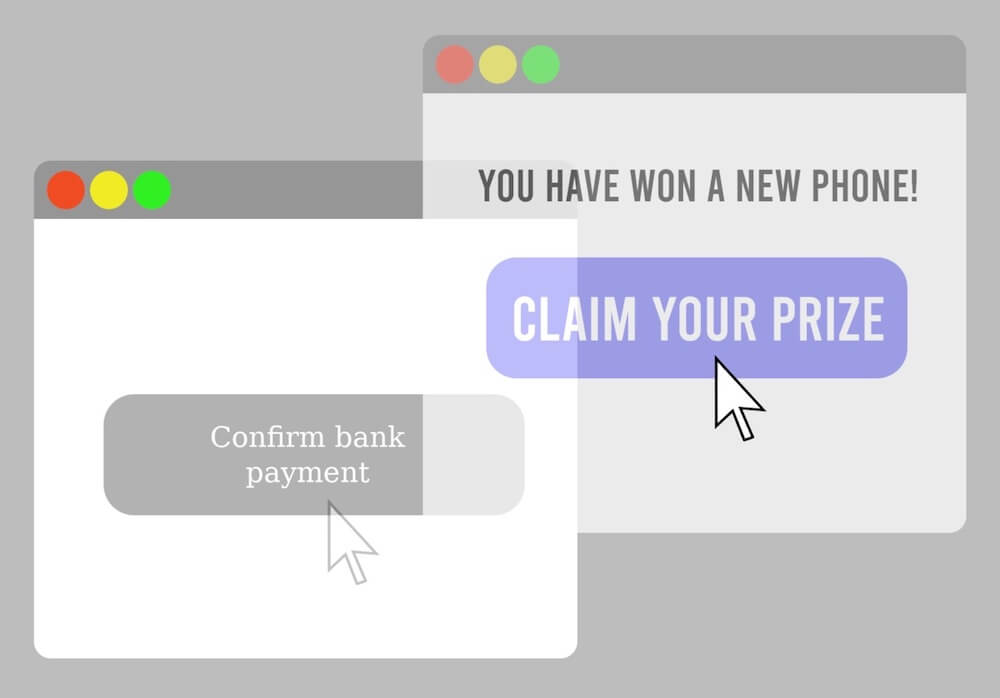
Common Security Threats to REST API
Here are some common threats that you should be aware of:
- Unauthorized access: This occurs when an attacker gains access to protected resources without the proper permissions. Implementing strong authorization and access control measures can help mitigate this risk.
- Brute force attacks: Attackers may try to guess API keys, access tokens, or user credentials through repeated trial and error. Implementing rate limiting and monitoring for suspicious activity can help detect and prevent brute force attacks.
Adopting Standardized Authorization Protocols
When it comes to REST API authorization, it’s a good idea to rely on established, standardized protocols. In this section, we’ll explore two widely-used protocols: OAuth 2.0 and OpenID Connect. Let’s dive in and see how these protocols can help you build secure APIs with robust authorization.
OAuth 2.0
Overview and Benefits: OAuth 2.0 is an industry-standard protocol for authorization, designed to provide secure access to protected resources on behalf of a user or an application. It enables third-party applications to obtain limited access to your API without sharing the user’s credentials. The benefits of using OAuth 2.0 include:
- Improved security: By using access tokens instead of user credentials, you minimize the risk of unauthorized access and credential leakage.
- Scalability: OAuth 2.0 is designed to work with various client types and platforms, making it easy to scale your API as needed.
- Flexibility: With different grant types, OAuth 2.0 can accommodate various authorization scenarios and use cases.
Grant Types: OAuth 2.0 supports several grant types, allowing you to tailor the authorization flow to your specific needs. The most common grant types include:
- Authorization Code: This grant type is suitable for web applications and involves a two-step process, where the user authorizes the app, and the app exchanges the authorization code for an access token.
- Implicit: This grant type is used for single-page applications (SPAs) and involves obtaining an access token directly from the authorization server.
- Resource Owner Password Credentials: This grant type involves the user providing their username and password directly to the app, which then exchanges them for an access token. It should only be used with trusted applications.
- Client Credentials: This grant type is suitable for machine-to-machine communication, where the app authenticates itself and obtains an access token without user intervention.
Token Management: Managing access tokens is an essential aspect of implementing OAuth 2.0. Key considerations include:
- Token expiration: Access tokens should have a limited lifetime, after which they expire and must be refreshed or reissued.
- Token revocation: You should provide a mechanism to revoke tokens in case of suspicious activity or when the user revokes access to the app.
- Token storage: Store tokens securely on the client-side to prevent unauthorized access or leakage.
OpenID Connect
Overview and Benefits: OpenID Connect (OIDC) is an identity layer built on top of OAuth 2.0, designed to enable user authentication and manage user identity. It’s a widely-adopted standard that helps you simplify user authentication and streamline the process of managing user accounts across multiple services. Benefits of using OpenID Connect include:
- Single Sign-On (SSO): Users can authenticate once and access multiple services without needing to log in again.
- Standardized user data: OIDC provides a standard set of user attributes, simplifying the integration process.
- Interoperability: OIDC is compatible with a wide range of platforms and services, making it easy to integrate with your existing infrastructure.
Integration with OAuth 2.0: Since OpenID Connect is built on top of OAuth 2.0, it extends the OAuth 2.0 authorization flow to include user authentication. OIDC introduces the concept of an ID token, which contains information about the user’s identity. This allows you to combine authentication and authorization in a single, streamlined process.
Identity Management: Implementing OIDC involves setting up an identity provider (IdP) that handles user authentication and manages user data.
Implementing Role-Based Access Control (RBAC)
Now that we’ve covered the standard authorization protocols, let’s talk about a powerful technique to manage access to your API resources: Role-Based Access Control (RBAC). This approach involves assigning specific permissions to user roles, making it easier to manage and enforce access policies across your API.
Importance of RBAC in REST API Security
RBAC is essential in building secure and maintainable APIs for several reasons:
- Simplified access management: By grouping permissions based on user roles, you can streamline the process of managing access rights, making it easier to understand and maintain.
- Scalability: As your API grows and evolves, RBAC allows you to accommodate new roles and permissions without significant effort.
- Principle of least privilege: RBAC helps you follow the principle of least privilege, ensuring that users only have access to the resources they need to perform their tasks.
Defining Roles and Permissions
To implement RBAC in your REST API, you’ll need to define roles and permissions:
- Roles: Roles represent a group of users with similar responsibilities or functions. For example, in an e-commerce API, you might have roles such as “Customer,” “Admin,” and “Vendor.” When defining roles, consider the various user types that interact with your API and the actions they need to perform.
- Permissions: Permissions define the specific actions a user can perform on an API resource. Examples of permissions include “CreateOrder,” “UpdateProduct,” and “DeleteUser.” When defining permissions, break down the operations your API supports and map them to the appropriate roles.
Enforcing RBAC at the API Level
Once you’ve defined the roles and permissions, it’s time to enforce the access control policies at the API level. Here are some tips to help you implement RBAC effectively:
- Middleware: Use middleware to intercept incoming API requests and enforce access control policies. Middleware can check the user’s role and associated permissions before allowing the request to proceed.
- Token-based access control: Include the user’s role information in the access token (e.g., an OAuth 2.0 access token or an OIDC ID token). This allows your API to verify the user’s role and permissions without additional database queries.
- Granular access control: Enforce access control at the resource level, rather than the entire API level. This ensures that users can only access the specific resources they are authorized to use.
- Centralized policy management: Store your RBAC policies in a centralized location, making it easier to update and maintain access control rules across your entire API.
Auditing and Monitoring REST API Authorization
Securing your REST API isn’t just about implementing authorization best practices; it’s also about continuously monitoring and auditing your API to ensure ongoing security. In this section, we’ll discuss the importance of logging and monitoring, real-time monitoring for suspicious activities, and regular security audits.
Importance of Logging and Monitoring
Logging and monitoring are crucial for maintaining the security and reliability of your REST API. They help you:
- Identify potential security threats: By analyzing logs and monitoring API activity, you can detect unusual patterns or unauthorized access attempts.
- Troubleshoot issues: Logs provide invaluable information to diagnose and resolve API issues, ensuring optimal performance and reliability.
- Maintain compliance: For organizations subject to regulatory requirements, logging and monitoring are essential for demonstrating compliance with security standards.
Real-time Monitoring for Suspicious Activities
Real-time monitoring is an essential aspect of securing your API, as it enables you to detect and respond to security threats as they occur. Here are some tips for implementing real-time monitoring for your API:
- Set up alerts: Configure alerts to notify you of any suspicious activities, such as repeated failed authentication attempts, unusual traffic patterns, or attempts to access restricted resources.
- Monitor access patterns: Analyze API access patterns to identify potential security risks, such as excessive data access or unauthorized access attempts.
- Integrate with security tools: Leverage security information and event management (SIEM) tools or other security platforms to analyze your API logs and detect potential threats.
Regular Security Audits
Conducting regular security audits is an essential part of maintaining a secure REST API. Security audits help you identify potential vulnerabilities and ensure that your API is adhering to the latest security best practices. Here are some key components of a successful security audit:
- Review access control policies: Regularly review and update your access control policies to ensure they are still relevant and appropriate for your current API functionality and user base.
- Vulnerability scanning: Use automated vulnerability scanning tools to identify potential security risks in your API, such as misconfigurations, outdated dependencies, or weak security controls.
- Penetration testing: Perform periodic penetration tests to simulate real-world attacks and assess your API’s ability to withstand security threats.
- Review audit logs: Analyze audit logs to identify trends, anomalies, or signs of unauthorized access, and take appropriate action to address any identified issues.
Security Best Practices for API Consumers
As an API consumer, you also have a responsibility to ensure that your interactions with APIs are secure.
Storing and Managing API Keys
API keys are a common method for authenticating API clients, and their security is of utmost importance. Here are some best practices for storing and managing API keys:
- Secure storage: Store API keys securely, using a dedicated secrets management system or environment variables. Never hard-code API keys in your source code or include them in publicly accessible files.
- Limit access: Restrict access to API keys only to the users and services that need them. This minimizes the risk of unauthorized access or accidental leakage.
- Regularly rotate keys: Regularly rotate your API keys to reduce the risk of unauthorized access in case a key is compromised.
Conclusion
In this blog post, we’ve covered essential REST API authorization best practices, touching on key topics such as the fundamentals of REST API authorization, standardized authorization protocols like OAuth 2.0 and OpenID Connect, implementing Role-Based Access Control, securing API endpoints, auditing and monitoring, and security practices for API consumers. The significance of adopting a proactive approach to REST API authorization cannot be overstated. By implementing robust security measures and continually monitoring and auditing your API, you can minimize the risk of unauthorized access, data breaches, and other security threats.
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.