· Alex · security · 12 min read
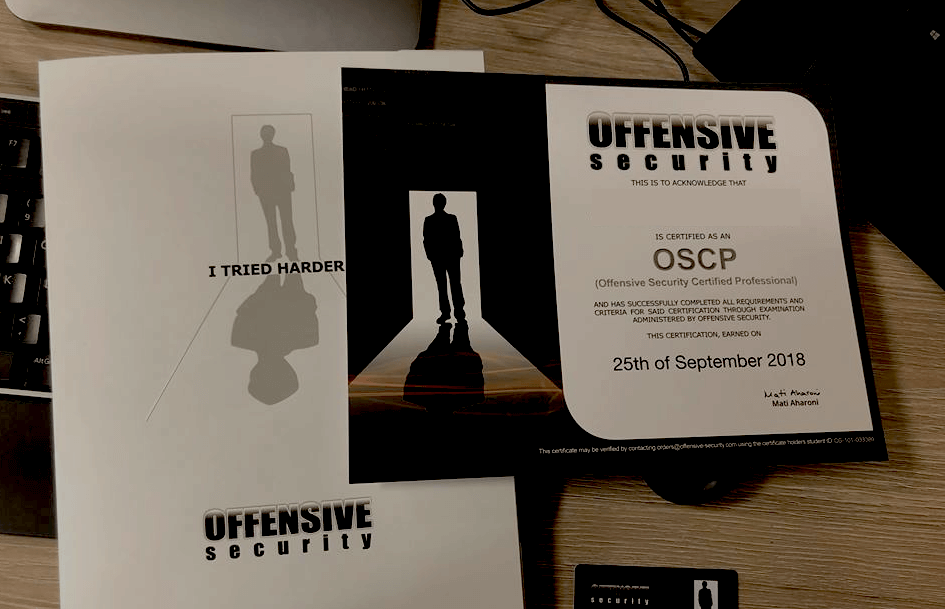
My OSCP Journey
Common questions, my experience, preparation and methodology as well as tips to help you land the OSCP exam
If you’re interested in more Offensive Security certifications, check out my reviews of the Offensive Security Web Expert, Offensive Security Exploit Developer and Offensive Security Experienced Penetration Tester courses and exams. Before diving into the article, here are the most common questions regarding the OSCP exam:
Is OSCP difficult?
- OSCP is considered an entry level certification. If you’re already in a penetration testing position or have good network and application security experience, it won’t be a problem for you. If you don’t, be prepared to put a few hundred hours of learning, but don’t worry as the course teaches you everything you need to know.
How many attempts are there for OSCP?
- You can take the OSCP exam as many times as you want, as long as you pay the OSCP exam retake fee.
Can we use Metasploit in OSCP?
- You can use Metasploit on a single exam machine, so my recommendation is to leave it as a last resort.
Can I Google during OSCP?
- Yes, you can search on Google, check out the course book or even the OffSec Discord.
Can I get a job after OSCP?
- There are entry level penetration testing, red-team and application-security jobs that ask for an OSCP. However, having the OSCP by itself won’t get you the job, only help you pass the initial recruiter screening.
Does OSCP expire?
- No, all Offensive Security certifications are permanent. You don’t have to pay 7K once every few years to be certified!
How long is OSCP course?
- Since the 2020 OSCP update, the minimum lab time you can buy is 90 days, which should be enough time to finish the course and the labs, even with the new machines.
What is the syllabus of OSCP exam?
How long will it take to prepare for the OSCP?
- Depends on your experience, and how much time you can invest in learning. I think 2 or 3 months are enough. I spent around 250 hours in OSCP learning, labs and doing HackTheBox machines.
What is the format of the OSCP exam?
- It’s a 24 hours online proctored exam with another 24 hours to write a professional report. Read more in the article below.
What positions would benefit from the OSCP?
- Penetration Testers, Product/Application Security Engineers, Security Operations, Red/Blue Team, QA Engineers
Preparing for the OSCP journey
Registration begins with choosing between 30, 60 or 90 days of lab time. Because my experience then was mostly in Software Engineering (rather than Cyber Security), I figured that I should get 90 days of lab time to have enough time to root all machines. Looking back now, 60 days would have been enough. But I guess it depends on how many hours you are able to invest into learning on a daily basis.
2020 update: now you can only get 90 days of lab time.
The first years of my IT career were spent as a System Administrator, which helped quite a bit during through the OSCP labs and OSCP exam. The key areas were basic OS usage and networking. Before taking on this challenge, I tried to build up my skills in the awesome hacker playground called HackTheBox. If you haven’t heard of it, make sure to check it out (hackthebox.eu). It’s free to join and you get access to 20 machines/targets you can attack and practice your skills on (in a legal and safe environment). Machines are rated by difficulty and you get a number of points for hacking each one. Every once in a while (weekly) a machine is retired, while another one is added. If you pay a subscription, you get access to the retired machines as well. The great thing about those machines, is that you can find plenty of write-ups online and see how others approached them.
Another great source of information is Ipsec’s youtube channel. Besides sharing a video walk-though of how he roots HackTheBox machines, he gives tons of tips and tricks along the way. So make sure to check it out! You could also try some Vulnhub machines. Vulnhub is a site where you can download vulnerable virtual machine you can hack. Just load the VM in VMware Player/VirtualBox and jump right into it. The goal of these VMs is to get root via any means possible. (Later update: VulnHub was acquired by Offensive Security). These resources prepared me very well for what was about to come. I think that if you manage to root all the active HTB machines for a couple of months, you should have no problem during the OSCP exam. Include all machines except the ones marked as “Insane”. Be aware that there’s usually a waiting time (1-2 weeks) between registering and the actual course start. On the first day you’ll be provided access to course materials, including the 8-hour PWK course videos, the ~400 page PWK PDF course, and your OSCP lab VPN access credentials.
The PWK Course
The materials you get cover a lot of topics, from Linux basics, buffer overflows to pivoting via SSH tunnels and Metasploit. You can find a link to the course syllabus in the questions section of this post (above) .You’ll get access to the Offensive Security Forum where you can find hints or ask for help as well as the Discord server. But most of the time you will have to do your own research to properly understand the issue. There will be countless things that you will still need to learn yourself during your time in the labs and the OSCP exam, so brush up on your Google-Fu!
The PWK Labs
The machines in the lab vary in difficulty. Some are easy enough, but others could take days to complete. The PWK Lab is designed like a real live enterprise network environment. This means that you have even simulated clients. So some machines can be compromised by client side attacks. Others might have information that can lead to the compromise of a different machine. As a general rule, never leave any stone unturned and always be thorough with your enumeration during Information gathering and Post-exploitation.
A big difference between the free labs from HackTheBox and OSCP, is that on the former the goal is to just get the flag that proves you’ve done it. That’s it. You don’t care about anything else after getting ROOT/SYSTEM and the flag. In the PWK labs and the OSCP exam, you have to act like in the real world: exploring the system after you have root may take more than actually exploiting it. But it’s worth it, as you find all kinds of goodies, just like in a real situation.
If you find yourself stuck, you can always access the Offensive Security Forum or Discord to ask for help. Don’t worry about that, it’s part of the learning process! Just don’t get upset if all you get is “Try Harder” - the Offensive Security mantra which you will love/hate. They also have a song for these situations. Give it a try when the motivation is low: https://www.offensive-security.com/offsec/say-try-harder/.
The OSCP Exam
The exam can be a brutal challenge due to its unusual 24h duration. You’ll have to keep notes, take screenshots, eat, drink and avoid going deep into rabbit holes. The exams goal is to prove that you have a good foundation of the penetration testing cycle. You will be allocated 6 machines, 5 exam machines and 1 Windows Test VM. Just like in the Labs, this VM will be your debugger for writing exploits. Using Metasploit is restricted to only one machine, so better save that as a last resort. You need to score 70/100 points to pass the exam. Be aware that automated tools like Nessus, OpenVAS or SQLmap are forbidden in the exam. Also make sure to read other journey’s out there and good luck on your OSCP exam!
My Experience with PWK Course & Lab
I spent a bit more than a week going through the entire PWK Course and doing the exercises. The latter helped cement the information, considering the number of new tools encountered. Documenting the exercises along with 10 lab machines, give 5 extra points in the exam so that’s welcomed. And it prepares you for the amount of notes you have to take.
I must say that documenting the exercises took me a lot more than expected, but I got better at it, as I got more organized. I used CherryTree for note taking. CherryTree is a hierarchical note taking tool which allows you to organize the information in a tree-like manner. It has all the good things you expect from a text editor (including exporting to HTML). As I was approaching the end of the pdf, I used my recon script to scan the entire lab and get an overview. The script is basically a collection of python scripts, developed over these last weeks which launch various Kali tools to enumerate services found in scans. This helped me go after the low hanging fruit first. Make sure to automate everything you can. It can save you tons of time! Note that some machines can be exploited in multiple ways, so you can return to them any point in your lab time. The lab is divided into 4 networks:
- Student/Public Network
- Dev Network
- IT Department
- Admin Department
You start in the Public Network and must make it all the way to the Admin Network, pivoting past 2 firewalls. This involves finding some “dual homed” machines (having multiple network adapters) with via which you can create SSH tunnels to the target networks. Similar to the root flag, you will find network flags that unlock networks in your Student Control Panel.
Takeaway from PWK Course & Lab
One of the things I’ve learned during my OSCP journey, is that SMB & SNMP protocols can be a particular rich source of information. And I spent a lot of time learning about privilege escalation. Getting root/admin access in the labs is usually done by making use of badly configured services (think like a lazy admin) versus using kernel exploits (which may cause system instability). As one should look for in the real world. Another thing I’ve learned a lot about is pivoting. Pivoting means using a compromised machine (the pivot) to be able to access a different one which only the pivot has access to. Basically using the first compromised machines to allow or aid in the compromise of other otherwise inaccessible (non-routable) systems. Simplest way to pivot is by using SSH tunnels and a tool like proxychains-ng or sshuttle. These allow you to run your scanning tools from your local machine as if you were connected directly to the target networks. Of course, all tools have limitations. For one thing, running things through proxies is slower, obviously. But there are other types of issues: certain nmap options won’t work via these types of channels, like the default option -sS (which does a type of fast port scanning, called SYN-Scanning).
But don’t worry, you will find ways to deal with that. The incredible feeling of accomplishment you get when compromising one of the harder hosts or unlock a new network, after days of trying, is hard to describe. After finishing the lab, I can say this: rooting your way through the machines is a thrilling experience. Although the software is a bit outdated (Update: Offensive Security updated OSCP in 2020), the lab helps you learn fundamental skills for a beginner pentester or anyone working in Security, as it gets you the proper mindset for attacking systems.
Exam Day
My approach to the OSCP exam was to fire up my recon script and let it do its thing. Knowing it will take at least an hour to complete, the plan was to start on the high point machines while that’s running. I also have more brain power in the morning, so I thought of using it carefully. Three hours in, I had administrative privileges on a first machine. Celebrated the quick achievement with a small victory break. Another three hours later, I got root on the other high point machine. With a good confidence boost and 50 points in the bag, I decide to take my lunch break. With almost 16 hours of exam time remaining and a relaxed mindset, I took on the 3rd target. After a few hours of trying hard with small progress (but no shell), I decided to move on to the next machine.
OSCP exam tip: rotating machines is key. Going straight for lots of hours on a single machine will burn you out and lower your morale (especially if you don’t make clear progress or reach milestones). After a few more hours I had rooted the other 2 machines. So almost 13 hours into the exam, I had rooted 4/5 machines and had (a theoretical) 80 points. After another break, I decide to review all the notes I had, make sure I have collected all the flags, submitted them in the exam panel, took enough screenshots, etc. Basically ensured that I had everything needed to create the exam report for those 4 machines. Once finished, I went back to that 3rd machine. And I’ve thrown everything at it, including Metasploit and after another 6-7 hours I got… nothing! Not even a low privilege shell! After so many hours spent on the machine, I was feeling something between annoyed, tired and stupid, so I decided to call it a day. I still had ~3 hours of exam time, but figured I should have enough points anyway.
The following day I wrote the report which ended up having 45 pages. This took me about 4-5 hours (and I had previously prepared a template). 36 hours later, I got the “You passed” email. Yey! I’m really proud of passing the OSCP exam!
Studying for OSCP was a challenging, but wonderful experience. Overall, I spent somewhere near 250 hours preparing, but it was definitely worth it!
About the Author:
Application Security Engineer and Red-Teamer. Over 15 years of experience in Application Security, Software Engineering and Offensive Security. OSCE3 & OSCP Certified. CTF nerd.



